Android Root Detection Bypass
Hi All
Introduction
The purpose of this post is to understand how I bypassed root detection while pen-testing an android apps. They were using rootbeer libraries to protect the application to run on rooted device.
In this post we will look at simple technique to bypass root detection. There are many module which are available for bypassing root detection. I used xposed module to bypass the root detection but it failed so I decided to try manually.
What is root detection?
Root Detection is an techniques which allow developer to control application to work only on Non rooted devise. Many Application does not run on rooted devise for security reason.
What is xposed module ?
Xposed is an framework which work on rooted devices. It provide various module which allow user to control the android devices.There are also few module which help to evade root detection logic which is been written in the application.
Step by Step approach to bypass root detection in the android application.
1. Reverse engineer the .apk with dex2jar.
dex2jar: It an small tool which allow to convert .apk into jar file
Command: dex2jar Android.apk
2. Search for root detection logic.
Once we reverse the file we need to open the file in JD-GUI we need to find the file in which root detection logic has been defined.
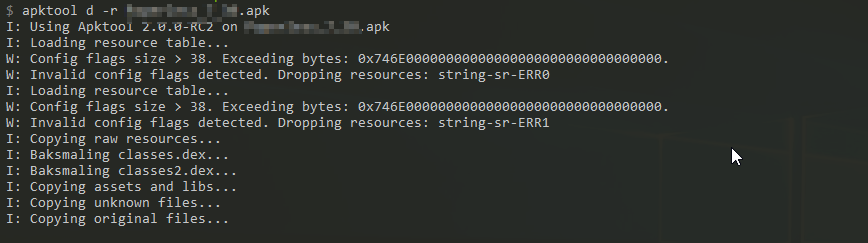
3. Reverse the apk with apktool.
apktool: A tool for reverse engineering 3rd party, closed, binary Android apps. It can decode resources to nearly original form and rebuild them after making some modifications. It also makes working with an app easier because of the project like file and automation of some repetitive tasks like building apk, etc.
Command: apktool d -r android.apk
4. Modify the code which contains the logic of detecting rooted device
Since we have reverse the code using apktool the complete code is available for modification into smali language. We can find all files which contains the root detection logic.
Open the file and change the name such as su, superuser, com.rootcloak to something random. Look into the screenshot below for the reference.
5. Rebuild the app with modified code.
We can find the rebuild code into dist folder in the current directory.
Command apktool b folder_name
6. Sign the apk file.
Once rebuild the entire folder with apktool we need to sign the apk using sign.jar.
Sign.jar file help us to sign the application with android test certificate.
Command: java -jar sign android.apk
Regards,
Sanket Solanki (aka m0nkeyshell)
Special Thanks to Sachit Bhatia (aka Thunder) & Chirag Savla (aka 3xpl01tc0d3r) for motivating me.
Introduction
The purpose of this post is to understand how I bypassed root detection while pen-testing an android apps. They were using rootbeer libraries to protect the application to run on rooted device.
In this post we will look at simple technique to bypass root detection. There are many module which are available for bypassing root detection. I used xposed module to bypass the root detection but it failed so I decided to try manually.
What is root detection?
Root Detection is an techniques which allow developer to control application to work only on Non rooted devise. Many Application does not run on rooted devise for security reason.
What is xposed module ?
Xposed is an framework which work on rooted devices. It provide various module which allow user to control the android devices.There are also few module which help to evade root detection logic which is been written in the application.
Step by Step approach to bypass root detection in the android application.
1. Reverse engineer the .apk with dex2jar.
dex2jar: It an small tool which allow to convert .apk into jar file
Command: dex2jar Android.apk
2. Search for root detection logic.
Once we reverse the file we need to open the file in JD-GUI we need to find the file in which root detection logic has been defined.
3. Reverse the apk with apktool.
apktool: A tool for reverse engineering 3rd party, closed, binary Android apps. It can decode resources to nearly original form and rebuild them after making some modifications. It also makes working with an app easier because of the project like file and automation of some repetitive tasks like building apk, etc.
Command: apktool d -r android.apk
4. Modify the code which contains the logic of detecting rooted device
Since we have reverse the code using apktool the complete code is available for modification into smali language. We can find all files which contains the root detection logic.
Open the file and change the name such as su, superuser, com.rootcloak to something random. Look into the screenshot below for the reference.
5. Rebuild the app with modified code.
We can find the rebuild code into dist folder in the current directory.
Command apktool b folder_name
6. Sign the apk file.
Once rebuild the entire folder with apktool we need to sign the apk using sign.jar.
Sign.jar file help us to sign the application with android test certificate.
Command: java -jar sign android.apk
Regards,
Sanket Solanki (aka m0nkeyshell)
Special Thanks to Sachit Bhatia (aka Thunder) & Chirag Savla (aka 3xpl01tc0d3r) for motivating me.










Hello your post is amazing and I like it so much it helps me to understand a lot of things which cover my curiosity and now you can visit my site: Archero Mod Apk
ReplyDeleteamazing article carrom pool mod apk it still working
ReplyDeleteHave you checked helpgurus.net for your Android games? Rodeo Stampede Mod APK for Android
ReplyDeleteTo root your device, use the KingRoot app now.
ReplyDeleteGame Injectors Hub: Explore a centralized hub for diverse Game injectors, providing a one-stop solution for enhancing your gaming experience across various titles.
ReplyDeleteI know the place to download RTS TV APK
ReplyDelete